Businesses handling data must always be on guard against data breaches – but individuals can also take measures to protect themselves. Data Breach Types can range from minor mistakes to large-scale attacks, and any leaks can result in severe consequences. Data breaches are widespread, with 39% of UK businesses reporting a cyber attack in 2022.
In this article, legal experts at Graham Coffey & Co. Solicitors will discuss the top 10 data breach categories individuals should be aware of, and how to implement robust safeguarding measures to reduce the risk of a breach of your data.
Data Breach Types – Human Error
Simple human mistakes are a leading cause of data breaches. Instances include emails with personal information sent to the wrong recipient or misplaced physical documents. Although these occurrences may not lead to severe breaches, it is crucial to mitigate any risk. Ensure data controllers understand their roles in protecting personal data and provide training for staff handling information.
Inadequate Control Procedures
Many businesses do not realise that altering personal data without permission can be considered a breach under certain circumstances. Breaches do not always result from hackers, but from businesses failing to establish proper data security measures.
Businesses designated as ‘data controllers’ under GDPR or the UK’s Data Protection Act 2018 must understand their responsibilities to protect stored or processed data, as failure to do so can lead to serious consequences.
If a breach exposes an individual’s data that results in a leak of sensitive information or tangible loss, they may be entitled to claim compensation. Anyone who suffers distress and financial loss due to a data breach should consult a data breach compensation solicitor for advice.
Password Guessing
In some cases, accessing private data requires little more than guessing a password or trying common variations. Data Breach Types can be caused by stolen credentials, which are the most frequent cause of data breaches, according to AAG.
Using simplistic and predictable passwords makes it easier for cybercriminals to gain unauthorised access to personal or professional accounts. To minimise this risk, create strong, unique passwords by mixing uppercase and lowercase letters, numbers, and special characters. Consider using a password management solution to store and produce passwords, and enabling multi-factor authentication (MFA) whenever it is available.
Unsecured Networks
The rise of remote work has led to increased reliance on cloud-based servers – but accessing data through unsecured networks, such as public WiFi, opens the doors to hackers.
Businesses should use secure cloud storage providers and ensure network security for remote data access. You should avoid connecting via public WiFi whenever possible.
Physical Theft
Stolen or misplaced devices can result in unauthorised access to personal data. To minimise this risk, enable device encryption, use password protection, and install remote wiping capabilities on all devices containing sensitive information. Additionally, maintain physical security measures and keep your devices secure at all times.
Phishing Data Breach
Cybercriminals employ deceptive emails or websites to lure users into revealing sensitive information or installing malware. To avoid falling for phishing scams, verify the legitimacy of emails, especially those requesting sensitive information or containing suspicious links.
You should educate yourself about phishing tactics and implement robust email filtering and security systems to minimise the risk.
Ransomware Data Breach
In a ransomware attack, a hacker locks a computer system and demands payment to release it. The breach itself and the potential sharing, selling, or use of the accessed information can have severe consequences.
Preventing ransomware involves employee awareness of phishing risks, installing firewalls, and providing necessary training to avoid mistakes that may lead to ransomware attacks.
Malware
Malware includes any software that allows hackers to access and control a device. Similar to ransomware, malware can serve various purposes, including stealing data or security credentials. In the event that an infiltrated device belongs to a network, the intruder might access additional devices within the system and potentially acquire passwords, allowing them to access accounts and data without being noticed.
In order to protect against malware, use dependable antivirus software, keep all software current, avoid clicking on suspicious links, and abstain from downloading files or applications from unconfirmed sources.
Public Wi-Fi Usage
Public Wi-Fi networks lacking proper security measures leave devices and data vulnerable to hackers who can intercept information transmitted across these networks. When using public Wi-Fi is necessary, safeguard your personal data by utilising a virtual private network (VPN) and turning off file-sharing features on your device.
Unauthorised Third-Party Access
Sharing login credentials or allowing unauthorised third parties to access sensitive data can lead to data breach types. Implement strict access controls, follow the principle of least privilege, and regularly review and update user permissions. Additionally, educate those with whom you are in contact about the dangers of sharing credentials and the importance of maintaining account security.
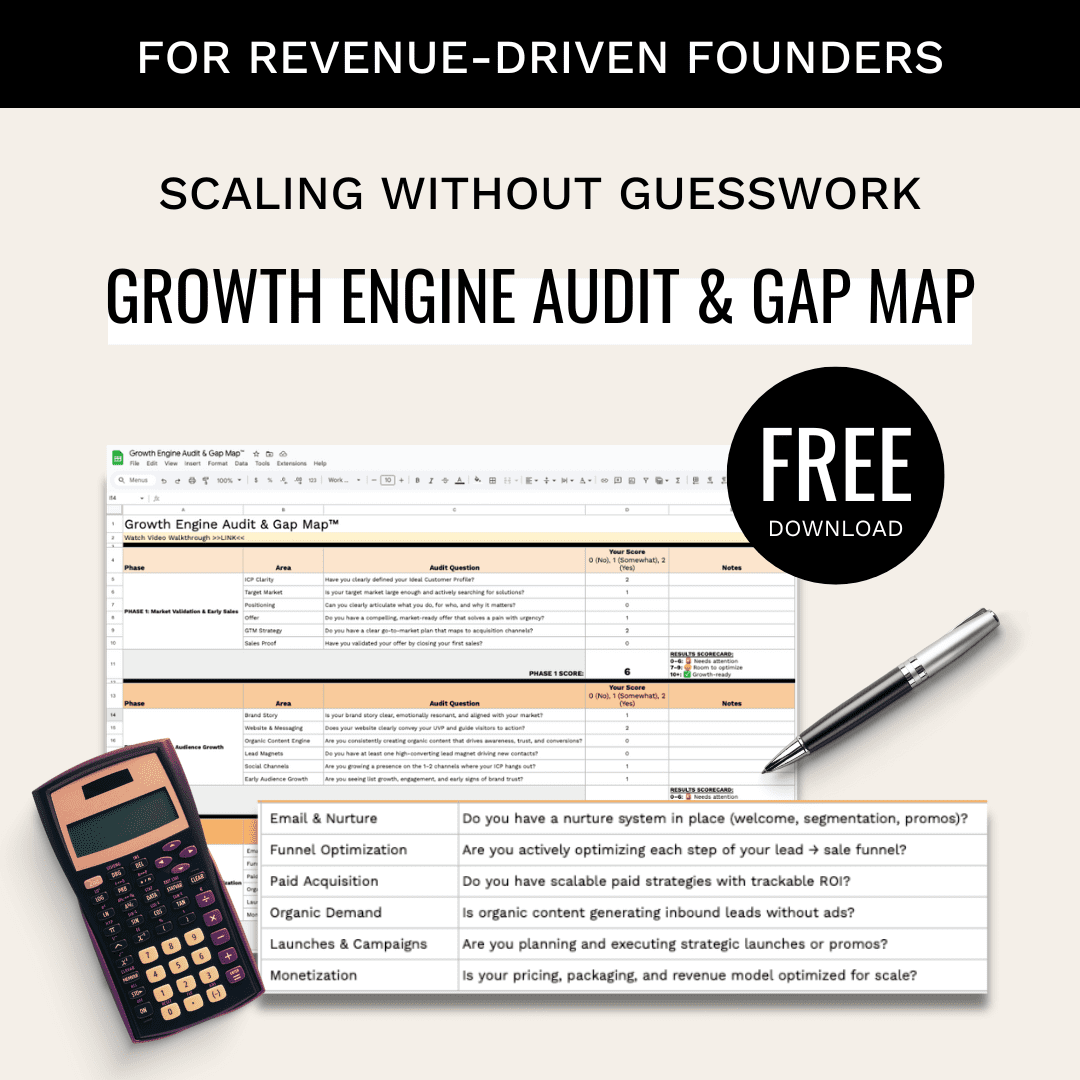
Want a clean, repeatable system for measuring B2B growth? Get the free Growth Metrics OS — a 6-day email course for technical founders and operators who want to measure growth and make better decisions.